World’s Biggest Cyber-Attack - WannaCry
As You may know , a major cyber attack known as WannaCry took place a few days ago. Dozens of companies, hospitals and even government agencies across the globe were targeted. Here we have a Complete Guide To The World’s Biggest Cyber-Attack That’s Happening Right Now in Pakistan and across the globe And How To Stay Safe From It.
 |
| World’s Biggest Cyber-Attack - WannaCry |
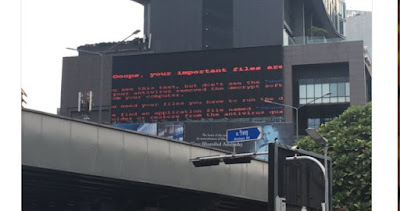 |
| Bangkok impacted by #WannaCry |
Billboard here in Bangkok that was impacted by #WannaCry
Pirates of The Caribbean 5 - WannaCry
According to a recent story published on the Hollywood Reporter Hackers have also threatened to release an upcoming Disney film on the internet if the studio doesn’t pay a heavy ransom in bitcoin. The movie in question is Pirates of The Caribbean 5.
If you are Not a an IT Guy and don't know much about these cyber attacks and terminologies don't worry we got you covered. lets have a look.
What is a Ransomware attack?
A ransomware infects a computer much like a traditional Malware. Don’t get a word I am sayin? Let me break it down in more simpler terms.
Once the virus has made its way into the computer it blocks access to all data. Instead screen pops up wherein the user is instructed to pay money.
The price usually increases with time with a corresponding countdown.
Your files are destroyed if the ransom amount isn’t paid on time. Sounds scary right?
According to Washington Post, this attack is particularly targeting Windows based devices, especially those that are still running Windows XP. Apple computers and Android devices appear not to be affected by WannaCry, but that does not mean that Macs or iPhones are immune to malware in general. Androids, especially, are susceptible if they’re running an older version of the Operating System.
In addition, you can:
 |
| #WannaCry screen grab. |
The only way is to secure your data is to not open such attachments in emails where you cant verify the sender. So do not open any email claiming that you have won US citizenship in lottery you never even participated in. Yea I know its tempting but no one is that lucky.
Once your computer is infected there is no way to secure access to the data except of paying the ones holding it hostage.
Once your computer is infected there is no way to secure access to the data except of paying the ones holding it hostage.
Mac users can chill however since WannaCry only attacks Windows operating system.
What can you do to stay safe from ransomware cyber attack?
While Pakistan has surprisingly not been affected that crazily yet, it’s good to take some precautionary measures so you don’t get affected by such things in the future.According to Washington Post, this attack is particularly targeting Windows based devices, especially those that are still running Windows XP. Apple computers and Android devices appear not to be affected by WannaCry, but that does not mean that Macs or iPhones are immune to malware in general. Androids, especially, are susceptible if they’re running an older version of the Operating System.
- So the first thing you need to do is, make your device software and operating systems are UP TO DATE.
In addition, you can:
- Create backups of your most important files, either by downloading them to an external hard drive or by storing them in a cloud-based storage service.
- Use a password manager to create and keep track of unique, hard-to-remember (and thus hard-to-break) passwords for each of your services. It’s a little counter-intuitive, but experts say it’s much more secure than the alternative, which is reusing the same password across multiple websites.
- Check your medical and credit reports for evidence of fraudulent activity.
- At work, check with your IT administrator to make sure your organization’s devices are protected from WannaCry.
- Remember to treat unexpected emails with caution, and read up on phishing — one of the most common types of social engineering attacks used by attackers to compromise machines.
Share your thoughts in Comments. Thank You,






Post a Comment